SOC 2 Vulnerability Scanning for On-Prem: Tiered Scanning Without Cloud-Native Tools
Every SOC 2 vulnerability scanning guide assumes the same starting point: connect a cloud-native scanner, enable automated assessments, and let the ...
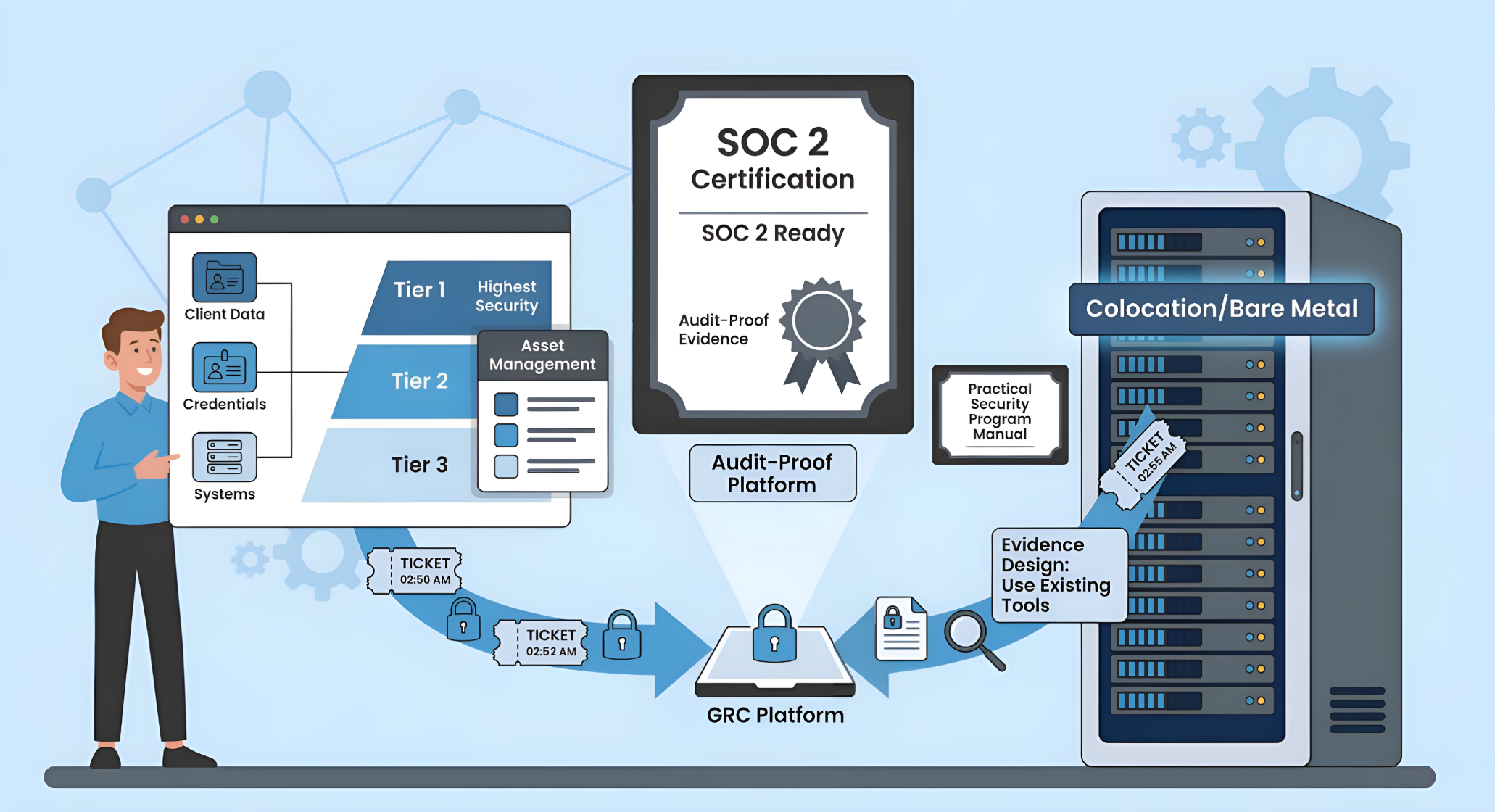
SOC 2 Readiness for Bare Metal SaaS: What to Expect When You Don't Run on AWS
A pattern keeps showing up. A SaaS company that has been running successfully for years, sometimes a decade or more, gets a call from a major ...
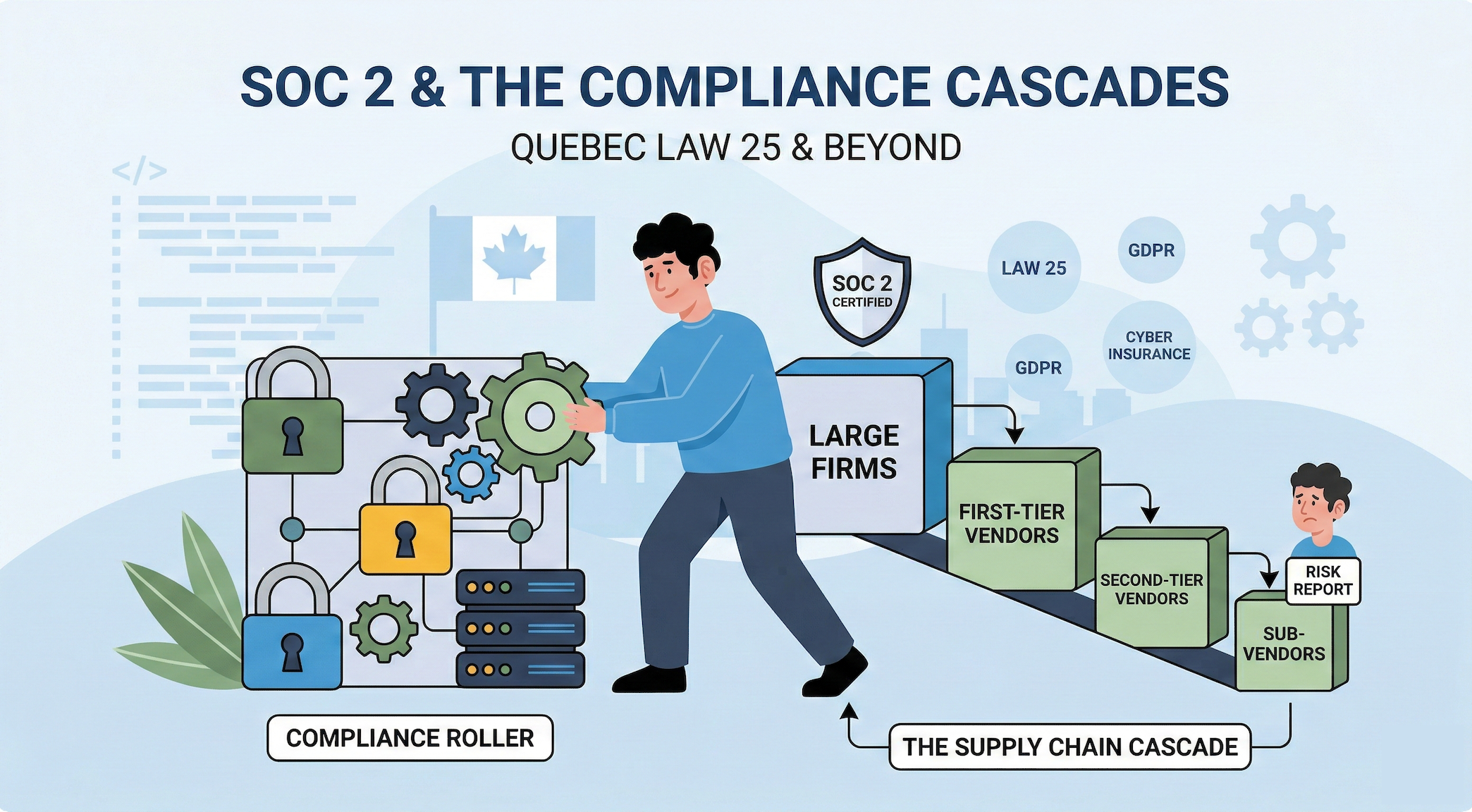
The SOC 2 Snowball: How Law 25 Is Pushing Compliance Down the Supply Chain
SOC 2, and compliance in general, is self-perpetuating. Once a company achieves certification, one of the first things the framework requires is ...
-1.png?width=100&height=100&name=Frame%20(5)-1.png)