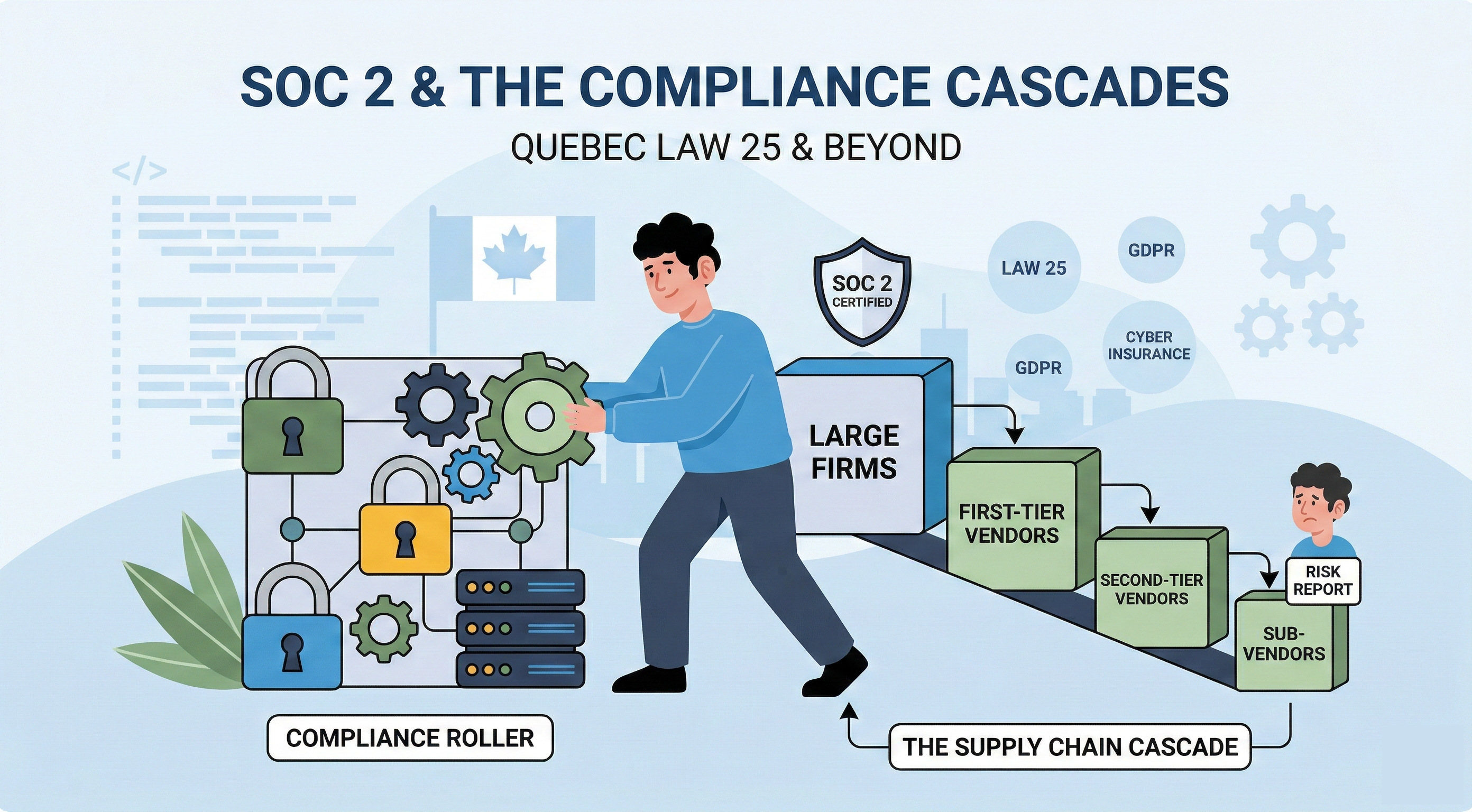
SOC 2, and compliance in general, is self-perpetuating. Once a company achieves certification, one of the first things the framework requires is assessing every vendor that touches their data. That assessment creates new compliance demand that didn't exist before - and it cascades down the supply chain faster than most companies realize.
The force accelerating this in Canada right now is Quebec's Law 25. Fully in effect since September 2024, Law 25 is Canada's closest equivalent to the EU's GDPR - and it has real teeth. Penal fines for severe violations reach up to $25 million CAD or 4% of worldwide turnover, whichever is higher, with fines doubling for repeat offenses. National players operating in Quebec - major insurers, banks, healthcare organizations - are now subject to these penalties, and their response has been predictable: formalize vendor oversight, demand evidence of controls, and push compliance requirements downstream to every vendor in the supply chain.
That downstream vendor is you. And this is the pattern playing out across every regulated industry in Canada right now.
How the Cascade Actually Works
Let's walk through the mechanics, because once you see it, you can't unsee it.
A major national insurer operating in Quebec is now directly subject to Law 25. Their legal and compliance teams know what $25 million in fines looks like, and they know the regulator is active - the Commission d'accès à l'information received 444 confidentiality incident reports in 2023-2024 alone. So they pursue SOC 2 to demonstrate they have real controls in place, not just policies on paper. Maybe their own enterprise clients demanded it. Maybe their cyber insurance carrier started asking harder questions. Maybe they lost a deal to a competitor who had the certification. Whatever the trigger, they go through the audit and come out the other side with a SOC 2 Type II report.
Here's what happens next, and this is the part most vendors miss.
SOC 2 isn't just about what you do internally. A core component of the Trust Services Criteria is vendor risk management. That national insurer is now required to assess every vendor that touches their data or systems. That's not optional. It's not a nice-to-have. It's a control their auditor will test every single year.
So they build out their vendor management program. They send questionnaires. They request evidence. They start sorting vendors into risk tiers. And the vendors in the highest tiers - the ones with access to production systems, customer data, or critical infrastructure - get a simple message: we need to see your SOC 2 report.
That vendor is you. A 15-person software shop, an IT consulting firm, a managed service provider. You've been delivering excellent work for this client for years. But now their compliance team needs documentation that your auditor has independently verified your controls - because their auditor is going to ask about it.
Now here's where the snowball picks up mass. You go through the process. You get your SOC 2. And suddenly you have a vendor management requirement of your own. You start looking at your subprocessors, your cloud providers, your SaaS tools, your outsourced dev team. You send them questionnaires. The ones that matter get the same message you got six months ago.
The cycle repeats. National enterprise to mid-market vendor to small vendor to their vendors. It doesn't stop.
This Isn't Theoretical — It's Happening Across Every Regulated Industry
If you serve customers in financial services, you've probably already felt this. Banks and financial institutions have been pushing compliance requirements downstream for years, but SOC 2 has become the common language. It used to be enough to fill out a self-assessment questionnaire and check some boxes. Those days are over. Procurement teams now have dedicated security reviewers, and "we take security seriously" doesn't cut it anymore.
Insurance is right behind them. The industry is getting hammered by regulators and cyber insurers simultaneously, and the response has been to formalize vendor oversight. If you're an IT consultant, a managed service provider, or a SaaS vendor serving insurance companies, the compliance questionnaires showing up in your inbox are going to keep getting longer and more specific.
Healthcare has its own version of this with HIPAA, but SOC 2 is increasingly layered on top. Organizations want to see both. They want HIPAA compliance and a SOC 2 report that demonstrates your controls are independently verified, not just self-attested.
And SaaS? SaaS is ground zero for the snowball effect. Every SaaS company that achieves SOC 2 immediately turns around and evaluates the dozens of tools in their own stack. If you're building software that other software companies use, the question isn't if you'll need SOC 2. It's whether you'll have it ready before your next renewal conversation.
Four Forces Making This Accelerate
This isn't just organic growth. There are specific forces pushing the snowball faster.
Privacy legislation is multiplying. Every new national, state / provincial, privacy law, every new international data regulation, every update to existing frameworks adds pressure. Companies responding to these regulations are standardizing on SOC 2 as a baseline because it covers a broad set of controls and it's recognized across industries. More regulation means more companies pursuing certification, which means more vendor assessments, which means more demand flowing downhill.
Buyers are getting more sophisticated. Five years ago, a startup's procurement process was "can you sign our MSA?" Today, even Series A companies have security review processes. The people running these reviews increasingly have compliance or security backgrounds. They know what a SOC 2 report looks like, they know what to look for, and they know when you're stalling.
Auditors are getting sharper. The auditors assessing your customers are paying closer attention to vendor management. They're not just checking that a vendor management policy exists — they're testing whether it's actually implemented. They want to see evidence that high-risk vendors were assessed, that issues were tracked, and that vendors without adequate controls were either remediated or replaced. Your customer's auditor is, in a very real sense, indirectly auditing you.
Cyber insurance is tightening the screws. Insurers are done writing policies based on a ten-question application. They want evidence of real controls, and they want to know that the companies they insure are managing their third-party risk. A SOC 2 report has become one of the fastest ways to satisfy an underwriter, which means more companies are pursuing it, which means more vendor assessments rolling downhill.
The Real Cost of Waiting
Here's what happens when you wait for the ask instead of getting ahead of it.
Your biggest customer sends the questionnaire. You don't have a SOC 2 report. You scramble to fill out a self-assessment. Their compliance team pushes back because self-attestation doesn't meet their auditor's requirements. You ask for an exception. Maybe you get one — for now. But that exception gets flagged in their next audit, and their auditor tells them it needs to be resolved.
Now you're in a contract renewal negotiation where compliance is a sticking point. Your customer likes your work. They don't want to switch vendors. But their auditor is breathing down their neck, and their board cares about risk. You're on a timeline you didn't choose, paying a premium for an accelerated readiness engagement because you need results in four months instead of twelve.
Meanwhile, your competitor — the one who started their SOC 2 journey a year ago — is winning the deals you're not even getting invited to. Because increasingly, the SOC 2 question isn't coming up during vendor review. It's coming up during vendor selection. If you don't have it, you don't make the shortlist.
Getting Ahead of the Wave
The smartest move is to start before anyone asks. Not because it's fun. Not because anyone is passionate about compliance frameworks. Because when that email inevitably arrives - and it will - the difference between responding with a PDF and responding with a panic is about twelve months of lead time.
What "getting ahead" actually looks like in practice:
- Start with a gap assessment. Figure out where the company stands today against the Trust Services Criteria. Most companies have more controls in place than they realize - MFA, access reviews, encryption in transit and at rest. The gap assessment reveals what's missing and produces a realistic timeline.
- Pick the right scope. SOC 2 is scoped to the systems and services relevant to customers. A focused scope means a faster, less painful process. Trying to include everything on day one is one of the most common mistakes, and it's entirely avoidable.
- Build the muscle, not just the checklist. The companies that extract the most value from SOC 2 treat it as an operating system upgrade, not a checkbox exercise. They bake security into workflows, automate evidence collection, and make compliance part of how they work rather than something they cram for once a year.
The Snowball Is Already Rolling
Every enterprise that achieves SOC 2 creates vendor assessment requirements that didn't exist before. Every mid-market company that responds to those requirements and gets certified creates more requirements for their own vendors. The surface area of compliance demand is expanding faster than most people realize.
For technical founders and IT leaders serving customers in insurance, financial services, healthcare, or SaaS - the wave is already here for some of you. The rest will feel it within the next twelve to eighteen months.
The companies that navigate this well are the ones that start before the pressure hits. Get the gap assessment done. Build a realistic timeline. And when that email from the biggest customer lands, be the vendor that responds in 24 hours with a clean report - not the one scrambling to explain why it doesn't exist yet.
The snowball doesn't care if you're ready. But your customers do.
If your team is navigating this right now, we help B2B SaaS companies build security programs that stay audit-ready without the quarterly scramble.
Ready to Build Your SOC 2 Roadmap?
Our free, no-obligation assessment will give you a clear, actionable plan to achieve compliance.
.png?width=155&height=82&name=Arrow%205%20(1).png)